

In the realm of high-security infrastructure—encompassing government agencies, defence command centres, and critical industrial facilities—standard IT procurement rules seldom apply. System Integrators (SIs) and Project Managers frequently encounter technical acronyms in tender documents that exceed typical consumer specifications.
One of the most crucial, yet often misunderstood terms, is TEMPEST.
When a project specification requests “TEMPEST-compliant hardware,” “low-emanation displays,” or “SCIF-ready endpoints,” it indicates that the environment deals with classified or highly sensitive information. In these situations, a standard commercial monitor is not only inadequate; it is a potential security risk.
This guide clarifies TEMPEST for technical professionals, examining NATO SDIP-27 standards, Red/Black separation, and why professional displays are central in the fight against electromagnetic espionage.
TEMPEST is a codename of the U.S. National Security Agency (NSA) and a NATO standard that refers to the investigation and study of Compromising Emanations (CEM).
It stands for: Telecommunications Electronics Material Protected from Emanating Spurious Transmission.
Every active electronic device generates an electromagnetic field (EMF) during operation.
For a display, this is known as Van Eck Phreaking. An attacker could theoretically reconstruct the image on your monitor without ever entering the room. TEMPEST standards ensure emissions are suppressed below the threshold of interception.
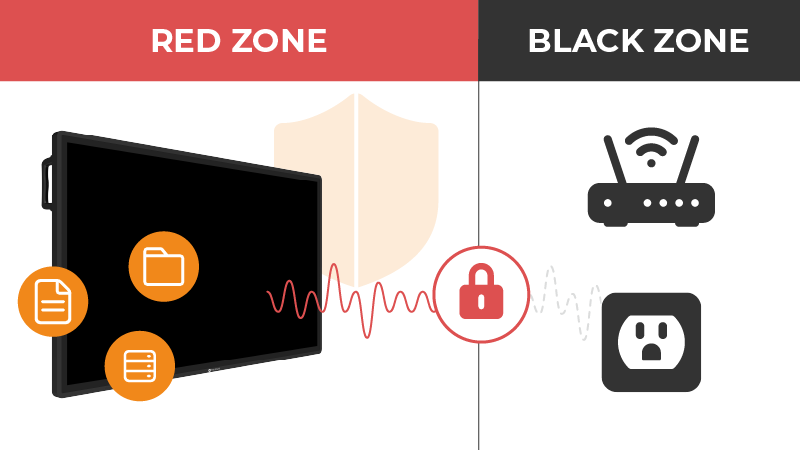
To understand TEMPEST in a system integration context, SIs must be familiar with the Red/Black architecture—a fundamental principle in secure facility design (such as SCIFs).
The Integration Challenge: The aim of TEMPEST engineering is to prevent “Red” signals from coupling onto “Black” lines. Professional secure displays are designed with internal isolation and specific grounding to maintain this separation within the device itself.
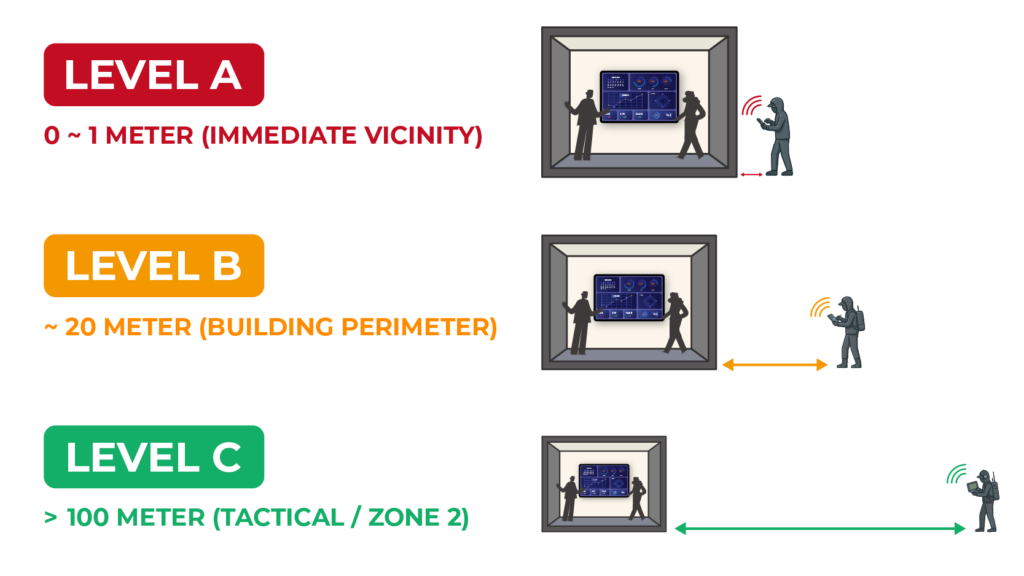
TEMPEST is graded based on “Zoning”—the physical security of the environment and the distance to a potential attacker. Most NATO allies use the SDIP-27 standard (formerly AMSG 720).
| NATO Standard (SDIP-27) | US Equivalent (NSA) | Risk Context | Assumed Distance | Requirement |
| Level A (FULMAR) | Level I | Immediate Risk | 0 ~ 1 Metre | Heavily modified, purpose-built hardware. |
| Level B (BREVEL) | Level II | Intermediate Risk | ~ 20 Metres | Rigorous metal shielding & grounding. |
| Level C (CONUS) | Level III | Low Risk | > 100 Metres | Robust professional-grade equipment. |
Key Takeaway for SIs:
While Level A requires certified specialised equipment, Level B and C environments often allow for “TEMPEST-ready” professional displays, which offer superior shielding without the exorbitant costs of Level A custom units.
In a Secure Compartmented Information Facility (SCIF), the monitor is a primary vulnerability for three reasons:
A common procurement mistake is to assume that regulatory compliance (FCC/CE) means security.
A plastic-cased consumer monitor can pass FCC Class B and still emit classified data to a receiver in the car park.

For Level B or C projects, SIs should look for these professional engineering characteristics:
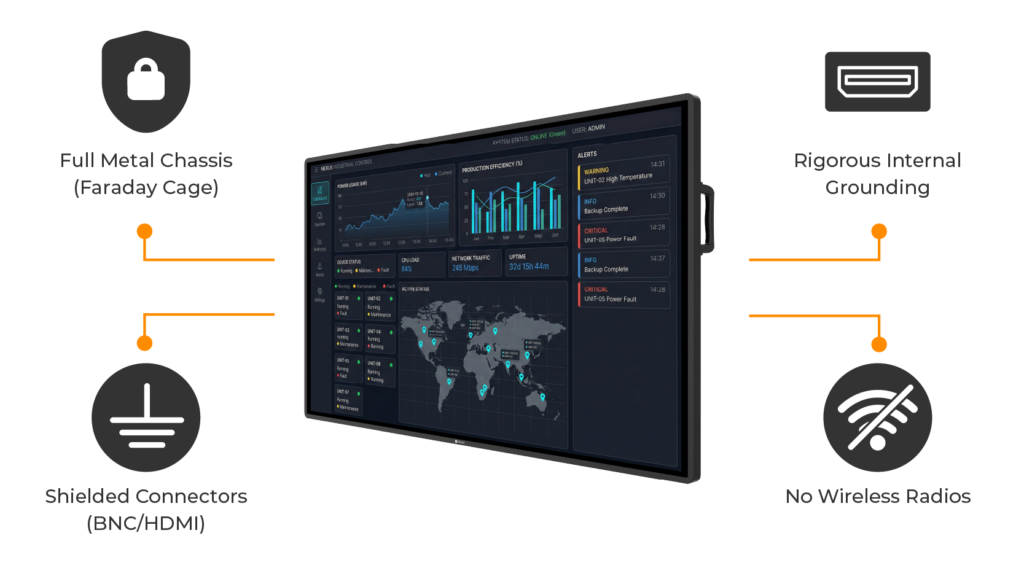
Understanding TEMPEST elevates a System Integrator from being a “hardware supplier” to a “security partner.” While Level A environments are specialised, the majority of secure projects require the “Good Hygiene Security” of Level B/C.
By selecting displays with metal chassis, rigorous grounding, and NDAA compliance, SIs provide a robust foundation for secure facilities—reducing risk and protecting the integrity of critical data. This is why AG Neovo remains the display choice of professionals.


